官方文档,https://kubernetes.io/docs/concepts/configuration/secret/
1. Secret基本概念
1.1 什么是Secret
Secret 资源的功能类似于 ConfigMap,但它专用于存放敏感数据,例如密码、数字证书、私钥、令牌 和 SSH key 等。
Secret 对象存储数据的方式及使用方式类似于 ConfigMap 对象,相同的是,都以键值方式存储数据,在 Pod 资源中通过环境变量或存储卷进行数据访问。不同的是,Secret 对象仅会被分发至调用了对象的 Pod 资源所在的工作节点,且只能由节点将其存储于内存中。另外,Secret 对象的数据的存储及打印格式为 Base64 编码的字符串,因此用户创建 Secret 对象时也要提供此编码格式的数据。在容器中以环境变量或存储卷的方式访问时,它们会被自动解码为明文格式。
需要注意的是,在 Master 节点上,Secret 对象以非加密的格式存储于 etcd 中,因此管理员必须加以精心管控以确保敏感数据的机密性,必须确保 etcd 集群节点间以及与 API Server 的安全通信,etcd 服务的访问授权,还包括用户访问 API Server 时的授权,因为拥有创建 Pod 资源的用户都可以使用 Secret 资源并能够通过 Pod 的容器访问其数据。
1.2 为何需要Secret
前面我们通过ConfigMap来实现应用与配置的解耦,但是解耦不仅仅只有配置文件,还应该有默认口令(例如MySQL、Redis服务访问的口令),用于SSL通信时的数字证书,用于认证的令牌和ssh key等,但这些敏感数据不适合存储在ConfigMap中,而是要用另一种被称为Secret的资源。将敏感数据存储在Secret中比明文存储在ConfigMap或Pod配置清单中更加安全。
1.3 Secret资源类别
Secret类似于ConfigMap资源,创建Secret对象也支持命令行、文件、目录等多种方式的数据源,而根据其存储格式及用途的不同,Secret对象还会划分为如下3种类别。
docker-registry:用于认证Docker Registry的Secret,以便于用户能使用私有容器镜像。generic:基于本地文件、目录或命令行创建的Secret,一般用于存储密码、秘钥、等信息。tls:基于指定的公钥和私钥对来创建TLSSecret,专用于TLS通信
[root@kube-master secret]# kubectl create secret
Create a secret using specified subcommand.
Available Commands:
docker-registry 创建一个给 Docker registry 使用的 secret
generic Create a secret from a local file, directory, or literal value
tls 创建一个 TLS secret
Usage:
kubectl create secret [flags] [options]
Use "kubectl <command> --help" for more information about a given command.
Use "kubectl options" for a list of global command-line options (applies to all commands).[root@kube-master secret]# kubectl create secret
Create a secret using specified subcommand.
Available Commands:
docker-registry 创建一个给 Docker registry 使用的 secret
generic Create a secret from a local file, directory, or literal value
tls 创建一个 TLS secret
Usage:
kubectl create secret [flags] [options]
Use "kubectl <command> --help" for more information about a given command.
Use "kubectl options" for a list of global command-line options (applies to all commands).1.4 Secret类型组成
- Opaque: 自定义数据内容:base64编码,用来存储密码、密钥、信息、证书等数据。
- kubernetes.io/tls: 用于为 SSL 通信模式存储证书和私钥文件,命令式创建时类型表示为 tls。
- kubernetes.io/dockerconfigjson: 用来存储 Docker 镜像仓库的认证信息,类型标识为 docker-registry。
- kubernetes.io/servcie-account-token: Servcie Account 的认证信息,可在创建 Service Account 时由 Kubernetes 自动创建。
💡 说明
base64编码并非加密机制,其编码的数据可使用 "base64 --decode" 一类的命令进行解码
1.5 Secret配置文件
- 与ConfigMap类似,区别在于Secret主要存储敏感数据,所有的数据要经过base64编码。
- 应用场景:凭据
- kubectl create secret 支持三种数据类型:
- docker-registry(kubernetes.io/dockerconfigjson):存储镜像仓库认证信息
- generic(Opaque):存储密码、密钥等
- tls(kubernetes.io/tls):存储TLS证书
2. 创建Secrets
帮助
kubectl explain secretkubectl explain secret2.1 基于命令创建Secret
- 帮助文档
kubectl create secret --helpkubectl create secret --help使用Secret为容器中运行的服务提供用于认证的用户名和密码是一种常见的应用场景,像MySQL镜像就支持通过环境变量来设置管理员用户的默认密码。
[root@kube-master secret]# kubectl create secret generic mysql-auth-secret --from-literal=username=root --from-literal=password=ikubernetes
generic ---> The name of the API generator to use.[root@kube-master secret]# kubectl create secret generic mysql-auth-secret --from-literal=username=root --from-literal=password=ikubernetes
generic ---> The name of the API generator to use.- 查看
[root@kube-master secret]# kubectl get secrets mysql-auth-secret
NAME TYPE DATA AGE
mysql-auth-secret Opaque 2 29m
#查看内容
[root@kube-master secret]# kubectl get secrets mysql-auth-secret -oyaml
apiVersion: v1
data:
password: aWt1YmVybmV0ZXM=
username: cm9vdA==
kind: Secret
metadata:
creationTimestamp: "2024-05-29T07:23:46Z"
name: mysql-auth-secret
namespace: default
resourceVersion: "1660181"
uid: f454b6d5-4aab-42fe-9bee-c44f91b17877
type: Opaque
#解密
echo aWt1YmVybmV0ZXM= | base64 -d[root@kube-master secret]# kubectl get secrets mysql-auth-secret
NAME TYPE DATA AGE
mysql-auth-secret Opaque 2 29m
#查看内容
[root@kube-master secret]# kubectl get secrets mysql-auth-secret -oyaml
apiVersion: v1
data:
password: aWt1YmVybmV0ZXM=
username: cm9vdA==
kind: Secret
metadata:
creationTimestamp: "2024-05-29T07:23:46Z"
name: mysql-auth-secret
namespace: default
resourceVersion: "1660181"
uid: f454b6d5-4aab-42fe-9bee-c44f91b17877
type: Opaque
#解密
echo aWt1YmVybmV0ZXM= | base64 -d2.2 基于⽂件创建Secret
Secret中包含Pod访问数据库所需的用户凭证,除了通过命令行创建,也可以通过文件方式创建;将用户名存储在文件./username.txt中,将密码存储在文件./password.txt中。
1.准备文件
[root@kube-master secret]# echo echo -n 'han' > ./username.txt
[root@kube-master secret]# echo -n '123456' > ./password.txt[root@kube-master secret]# echo echo -n 'han' > ./username.txt
[root@kube-master secret]# echo -n '123456' > ./password.txt2.通过kubectl create secret 命令将这些⽂件打包成⼀个Secret 对象
[root@kube-master secret]# kubectl create secret generic mysql-auth-secrets --from-file=./username.txt --from-file=./password.txt
secret/mysql-auth-secrets created
#查看
[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
mysql-auth-secrets Opaque 2 50s[root@kube-master secret]# kubectl create secret generic mysql-auth-secrets --from-file=./username.txt --from-file=./password.txt
secret/mysql-auth-secrets created
#查看
[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
mysql-auth-secrets Opaque 2 50s2.3 基于TLS Secret
为Nginx应⽤创建SSL虚拟主机时,需要先通过Secret对象向容器注⼊服务器证书,以供nginx进程加载使⽤
- 帮助文档
kubectl create tls --helpkubectl create tls --help1.准备⼀个⾃签证书
#生成key
openssl genrsa -out nginx.key 2048
#生成crt
openssl req -new -x509 -key nginx.key -out nginx.crt -subj "/C=CN/ST=BJ/L=BJ/O=DevOps/CN=book.ikubernetes.net"#生成key
openssl genrsa -out nginx.key 2048
#生成crt
openssl req -new -x509 -key nginx.key -out nginx.crt -subj "/C=CN/ST=BJ/L=BJ/O=DevOps/CN=book.ikubernetes.net"2.创建tls类型的secret资源
[root@kube-master secret]# kubectl create secret tls nginx-tls-secret --key=nginx.key --cert=nginx.crt
secret/nginx-tls-secret created[root@kube-master secret]# kubectl create secret tls nginx-tls-secret --key=nginx.key --cert=nginx.crt
secret/nginx-tls-secret created3.查看
[root@kube-master secret]# kubectl get secrets nginx-tls-secret -oyaml
apiVersion: v1
data:
tls.crt: ......
tls.key: ......
kind: Secret
metadata:
creationTimestamp: "2024-05-30T07:21:11Z"
name: nginx-tls-secret
namespace: default
resourceVersion: "1729408"
uid: 7dca0a90-822f-43e9-95f1-be1a7f6346c0
type: kubernetes.io/tls[root@kube-master secret]# kubectl get secrets nginx-tls-secret -oyaml
apiVersion: v1
data:
tls.crt: ......
tls.key: ......
kind: Secret
metadata:
creationTimestamp: "2024-05-30T07:21:11Z"
name: nginx-tls-secret
namespace: default
resourceVersion: "1729408"
uid: 7dca0a90-822f-43e9-95f1-be1a7f6346c0
type: kubernetes.io/tls💡 说明
⽆论⽤户提供的证书是什么名称,最终都会转为tls.key私钥 tls.crt公钥
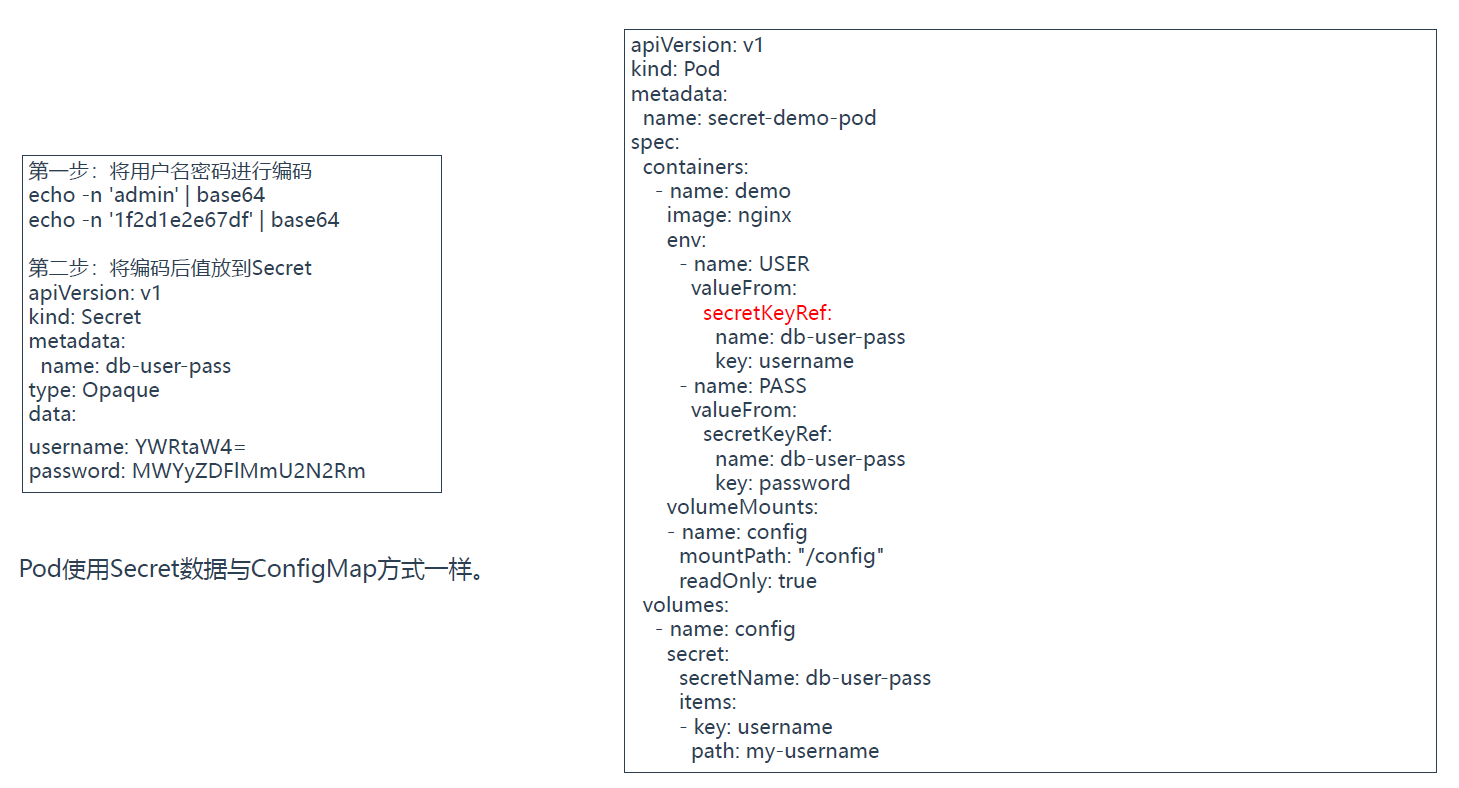
2.4 基于清单式创建
Secret 资源是标准的 Kubernetes API 对象,除了标准的 apiVersion、kind 和 metadata 字段,它可用的其他字段具体如下:
data <map[string]string>: "key:value" 格式的数据,通常是敏感信息,数据格式需是以 Base64 格式编码的字符串,因此需要用户事先先完成编码。stringData <map[string]string>: 以明文格式(非 Base64 编码)定义的 "key:value" 数据;无须用户事先对数据进行 Base64 编码,而是在创建为 Secret 对象时自动进行编码并保存于 data 字段中,stringData 字段中明文不会被 API Server 输出,不过若是使用 "kubectl apply" 命令进行的创建,那么注解信息中还是可能会直接输出这些信息的。type <string>: 仅是为了便于编程方式处理 Secret 数据而提供的类型标识。
明文
[root@kube-master secret]# cat redis-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secret-demo
stringData:
username: redis
password: redis@123
type: Opaque[root@kube-master secret]# cat redis-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secret-demo
stringData:
username: redis
password: redis@123
type: Opaque加密
[root@kube-master secret]# echo -n "admin" | base64
YWRtaW4=
[root@kube-master secret]# echo -n "123456" | base64
MTIzNDU2[root@kube-master secret]# echo -n "admin" | base64
YWRtaW4=
[root@kube-master secret]# echo -n "123456" | base64
MTIzNDU2[root@kube-master secret]# cat secret-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secre-hello
data:
user: YWRtaW4=
password: MTIzNDU2[root@kube-master secret]# cat secret-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secre-hello
data:
user: YWRtaW4=
password: MTIzNDU23. Pod引用Secret
- 帮助文档
kubectl explain pod.spec.imagePullSecretskubectl explain pod.spec.imagePullSecrets3.1 Secret存储卷
类似于 Pod 使用 ConfigMap 对象的方式,Secret 对象可以注入为环境变量,也可以存储为卷形式挂载使用
除了其类型及引⽤的标识需要替换为 secret、secretName之外,其他⼏乎⼀致,包括⽀持使⽤挂载整个存储卷,只挂载存储卷中指定的键值等
1.查看tls
[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
nginx-tls-secret kubernetes.io/tls 2 60m[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
nginx-tls-secret kubernetes.io/tls 2 60m2.创建
[root@kube-master secret]# cat secret-volume-demo.yaml
apiVersion: v1
kind: Pod
metadata:
name: my-pod-demo
spec:
volumes:
- name: my-volume #定义挂载名字,让volumMounts使用
secret:
secretName: nginx-tls-secret
containers:
- name: my-container-demo
image: nginx:latest
ports:
- containerPort: 80
volumeMounts:
- name: my-volume
mountPath: /etc/nginx/ssl
readOnly: true[root@kube-master secret]# cat secret-volume-demo.yaml
apiVersion: v1
kind: Pod
metadata:
name: my-pod-demo
spec:
volumes:
- name: my-volume #定义挂载名字,让volumMounts使用
secret:
secretName: nginx-tls-secret
containers:
- name: my-container-demo
image: nginx:latest
ports:
- containerPort: 80
volumeMounts:
- name: my-volume
mountPath: /etc/nginx/ssl
readOnly: true3.执行
kubectl apply -f secret-volume-demo.yamlkubectl apply -f secret-volume-demo.yaml4.验证效果
[root@kube-master secret]# kubectl exec -it my-pod-demo -- ls /etc/nginx/ssl
tls.crt tls.key[root@kube-master secret]# kubectl exec -it my-pod-demo -- ls /etc/nginx/ssl
tls.crt tls.key3.2 通过环境变量
Pod资源以环境变量⽅式获取Secret数据,存在两种⽅式
- 将指定键的值传递给环境变量,一个一个传递,通过
env.valueFrom字段实现; - 将Secret对象上的全部键一次性全部映射为容器的环境变量,通过
envFrom字段实现;
env
1.创建secret
[root@kube-master secret]# cat secret-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secre-hello
data:
user: YWRtaW4=
password: MTIzNDU2[root@kube-master secret]# cat secret-demo.yaml
apiVersion: v1
kind: Secret
metadata:
name: secre-hello
data:
user: YWRtaW4=
password: MTIzNDU22.创建pod
[root@kube-master secret]# cat secret-env.yaml
apiVersion: v1
kind: Pod
metadata:
name: my-pod-demo1
spec:
containers:
- name: my-container
image: nginx:latest
ports:
- containerPort: 80
env:
- name: USER
valueFrom:
secretKeyRef:
name: secre-hello
key: user[root@kube-master secret]# cat secret-env.yaml
apiVersion: v1
kind: Pod
metadata:
name: my-pod-demo1
spec:
containers:
- name: my-container
image: nginx:latest
ports:
- containerPort: 80
env:
- name: USER
valueFrom:
secretKeyRef:
name: secre-hello
key: user3.验证
[root@kube-master secret]# kubectl exec -it my-pod-demo1 -- /bin/bash
root@my-pod-demo1:/# env | egrep -i "(user|pass)"
USER=admin[root@kube-master secret]# kubectl exec -it my-pod-demo1 -- /bin/bash
root@my-pod-demo1:/# env | egrep -i "(user|pass)"
USER=adminenvFrom
apiVersion: v1
kind: Pod
metadata:
name: my-pod-demo1
spec:
containers:
- name: my-container
image: nginx:latest
ports:
- containerPort: 80
envFrom: # 整体引⽤指定的Secret对象全部键名和键值
- prefix: New # 将所有键名引⽤为环境变量时统⼀添加的前缀 (⽆需求,可不⽤)
secretRef:
name: secre-helloapiVersion: v1
kind: Pod
metadata:
name: my-pod-demo1
spec:
containers:
- name: my-container
image: nginx:latest
ports:
- containerPort: 80
envFrom: # 整体引⽤指定的Secret对象全部键名和键值
- prefix: New # 将所有键名引⽤为环境变量时统⼀添加的前缀 (⽆需求,可不⽤)
secretRef:
name: secre-hello4. imagePullSecret 资源对象
官方文档,
https://kubernetes.io/zh-cn/docs/tasks/configure-pod-container/pull-image-private-registry/
https://kubernetes.io/zh-cn/docs/concepts/configuration/secret/#using-imagepullsecrets
当Pod配置清单中定义的容器镜像来自于私有仓库时,需要先认证目标的Registry,而后才能正常下载镜像,imagePulLSecret字段指定认证Registry时使用的Secret对象,以辅助kubelet从需要认证的私有仓库获取镜像。
创建用于认证Registry的Secret,有专用的docker-registry子命令,通常认证需要向kubeLet提供Registry地址、用户名、密码、Email信息,因此docker-registry子命令需要同时使用以下4个选项。
--docker-server:用于指定私有仓库服务器地址;
--docker-User:用于指定私有仓库认证的用户名;
--docker-password:用于指定私有仓库认证的密码;
--dcker-email:用于指定请求私有仓库的用户E-mail(可选)
1.创建aliyun-registry的Secret对象
kubectl create secret docker-registry local-registry --docker-username=admin --docker-password=admin@123kubectl create secret docker-registry local-registry --docker-username=admin --docker-password=admin@123- 或者声明文件
apiVersion: v1
data:
.dockerconfigjson: ...
kind: Secret
metadata:
name: local-registry
type: kubernetes.io/dockerconfigjsonapiVersion: v1
data:
.dockerconfigjson: ...
kind: Secret
metadata:
name: local-registry
type: kubernetes.io/dockerconfigjson解密
kubectl get secret regcred --output="jsonpath={.data.\.dockerconfigjson}" | base64 -d
{"auths":{"registry.cn-zhangjiakou.aliyuncs.com":{"username":"hsuing.han@outlook.com","password":"123456","email":"hsuing.han@outlook.com","auth":"aHN1aW5nLmhhbkBvdXRsb29rLmNvbTpoeDEzMjMxMj"}}}
#查看用户和密码
echo aHN1aW5nLmhhbkBvdXRsb29rLmNvbTpoeDEzMjMxMj |base64 -d
#或者,拿到.dockerconfigjson进行
echo ...|base64 -d
#对auth 加密
echo han:123456 |base64kubectl get secret regcred --output="jsonpath={.data.\.dockerconfigjson}" | base64 -d
{"auths":{"registry.cn-zhangjiakou.aliyuncs.com":{"username":"hsuing.han@outlook.com","password":"123456","email":"hsuing.han@outlook.com","auth":"aHN1aW5nLmhhbkBvdXRsb29rLmNvbTpoeDEzMjMxMj"}}}
#查看用户和密码
echo aHN1aW5nLmhhbkBvdXRsb29rLmNvbTpoeDEzMjMxMj |base64 -d
#或者,拿到.dockerconfigjson进行
echo ...|base64 -d
#对auth 加密
echo han:123456 |base642.查看secret,资源类型为kubernetes.io/dockerconfigjson
[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
local-registry kubernetes.io/dockerconfigjson 1 47s[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
local-registry kubernetes.io/dockerconfigjson 1 47s3.Pod引用Secret资源;
imagePullSecret在spec字段中;和container是平级的;
kubectl explain pod.spec.imagePullSecrets
KIND: Pod
VERSION: v1
RESOURCE: imagePullSecrets <[]Object>
DESCRIPTION:
ImagePullSecrets is an optional list of references to secrets in the same
namespace to use for pulling any of the images used by this PodSpec. If
specified, these secrets will be passed to individual puller
implementations for them to use. For example, in the case of docker, only
DockerConfig type secrets are honored. More info:
https://kubernetes.io/docs/concepts/containers/images#specifying-imagepullsecrets-on-a-pod
LocalObjectReference contains enough information to let you locate the
referenced object inside the same namespace.
FIELDS:
name <string>
Name of the referent. More info:
https://kubernetes.io/docs/concepts/overview/working-with-objects/names/#nameskubectl explain pod.spec.imagePullSecrets
KIND: Pod
VERSION: v1
RESOURCE: imagePullSecrets <[]Object>
DESCRIPTION:
ImagePullSecrets is an optional list of references to secrets in the same
namespace to use for pulling any of the images used by this PodSpec. If
specified, these secrets will be passed to individual puller
implementations for them to use. For example, in the case of docker, only
DockerConfig type secrets are honored. More info:
https://kubernetes.io/docs/concepts/containers/images#specifying-imagepullsecrets-on-a-pod
LocalObjectReference contains enough information to let you locate the
referenced object inside the same namespace.
FIELDS:
name <string>
Name of the referent. More info:
https://kubernetes.io/docs/concepts/overview/working-with-objects/names/#names4.引入imagePullSecrets
#需要创建hub仓库的secret
kubectl create secret docker-registry docker-regsitry-auth --docker-server="hub.cropy.cn" --docker-username="admin" --docker-password="Harbor12345" -n test#需要创建hub仓库的secret
kubectl create secret docker-registry docker-regsitry-auth --docker-server="hub.cropy.cn" --docker-username="admin" --docker-password="Harbor12345" -n testapiVersion: apps/v1
kind: Deployment
metadata:
name: java-demo
namespace: test
spec:
replicas: 2
selector:
matchLabels:
project: www
app: java-demo
template:
metadata:
labels:
project: www
app: java-demo
spec:
imagePullSecrets:
- name: "docker-regsitry-auth"
containers:
- image: hub.cropy.cn/demo/java-demo:v1
name: java-demo
imagePullPolicy: Always
ports:
- containerPort: 8080
name: web
protocol: TCP
resources:
requests:
cpu: 0.5
memory: 0.5Gi
limits:
cpu: 1
memory: 2Gi
livenessProbe:
httpGet:
path: /
port: 8080
initialDelaySeconds: 60
timeoutSeconds: 20
readinessProbe:
httpGet:
path: /
port: 8080
initialDelaySeconds: 60
timeoutSeconds: 20apiVersion: apps/v1
kind: Deployment
metadata:
name: java-demo
namespace: test
spec:
replicas: 2
selector:
matchLabels:
project: www
app: java-demo
template:
metadata:
labels:
project: www
app: java-demo
spec:
imagePullSecrets:
- name: "docker-regsitry-auth"
containers:
- image: hub.cropy.cn/demo/java-demo:v1
name: java-demo
imagePullPolicy: Always
ports:
- containerPort: 8080
name: web
protocol: TCP
resources:
requests:
cpu: 0.5
memory: 0.5Gi
limits:
cpu: 1
memory: 2Gi
livenessProbe:
httpGet:
path: /
port: 8080
initialDelaySeconds: 60
timeoutSeconds: 20
readinessProbe:
httpGet:
path: /
port: 8080
initialDelaySeconds: 60
timeoutSeconds: 20或者
# 配置.docker/config.json文件,包含了与 Docker Hub 或其他私有仓库进行身份验证所需的凭据信息。
cat ~/.docker/config.json
{
"auths": {
"registry.test.com": {
"auth": "dmlwZXIucm9ib3QuZG9ja2VyOlNUYW"
}
}
}
# 创建secret给pod使用
kubectl create secret generic <secret-name> --from-file=.dockerconfigjson=.docker/config.json --type=kubernetes.io/dockerconfigjson
# 这里,创建的secret可以在pod中通过imagePullSecrets引用# 配置.docker/config.json文件,包含了与 Docker Hub 或其他私有仓库进行身份验证所需的凭据信息。
cat ~/.docker/config.json
{
"auths": {
"registry.test.com": {
"auth": "dmlwZXIucm9ib3QuZG9ja2VyOlNUYW"
}
}
}
# 创建secret给pod使用
kubectl create secret generic <secret-name> --from-file=.dockerconfigjson=.docker/config.json --type=kubernetes.io/dockerconfigjson
# 这里,创建的secret可以在pod中通过imagePullSecrets引用4.1 ImagePullPolicy
官方文档: https://kubernetes.io/zh-cn/docs/concepts/containers/images/
在指定容器镜像时,必须要提供镜像值(Image Value)这是一个供容器运行时(如Containerd)从镜像仓库拉取镜像的地址; 关键配置: ImagePullPolicy和ImagePullSecrets这两个都是供容器运行时使用的;
imagePullPolicy设置的是kubernetes节点拉取镜像策略,这个设置很重要。它有三个值可以设置,Always、Never、IfNotPresent;
- IfNotPresent: 本地有镜像则使用本地镜像,本地不存在则拉取镜像;(默认值)
- Always: 每次都尝试拉取镜像,忽略容器运行时维护的所有本地缓存;
- Never: 永不拉取,禁止从仓库下载镜像,如果本地镜像已经存在,kubelet会尝试启动容器,否则,启动失败;
查看属性
kubectl explain pod.spec.containers.imagePullPolicy
KIND: Pod
VERSION: v1
FIELD: imagePullPolicy <string>
DESCRIPTION:
Image pull policy. One of Always, Never, IfNotPresent. Defaults to Always
if :latest tag is specified, or IfNotPresent otherwise. Cannot be updated.
More info:
https://kubernetes.io/docs/concepts/containers/images#updating-imageskubectl explain pod.spec.containers.imagePullPolicy
KIND: Pod
VERSION: v1
FIELD: imagePullPolicy <string>
DESCRIPTION:
Image pull policy. One of Always, Never, IfNotPresent. Defaults to Always
if :latest tag is specified, or IfNotPresent otherwise. Cannot be updated.
More info:
https://kubernetes.io/docs/concepts/containers/images#updating-images案例
cat httpdpod-test.yaml
apiVersion: v1
kind: Pod
metadata:
name: httpd-testpod
namespace: default
spec:
containers:
- name: httpd
image: nginx
imagePullPolicy: IfNotPresentcat httpdpod-test.yaml
apiVersion: v1
kind: Pod
metadata:
name: httpd-testpod
namespace: default
spec:
containers:
- name: httpd
image: nginx
imagePullPolicy: IfNotPresent5. ServiceAccount拉取私有镜像
可以通过ImagPullPolicy和ImageullSecrets指定下载镜像的策略,ServiceAccount也可以基于
spec.imagePullSecret字段附带一个由下载镜像专用的Secret资源组成的列表,用于在容器创建时,从某个私有镜像仓库下载镜像文件之前的服务认证
5.2 创建Secrets资源
这里根据自己的实际去定义即可;一定要是对的地址和认证信息;否则无法pull/push
kubectl create secret docker-registry \
aliyun-registry \
--docker-server=registry.cn-hangzhou.aliyuncs.com \
--docker-username=xxxxxxx \
--docker-password=xxxxxxkubectl create secret docker-registry \
aliyun-registry \
--docker-server=registry.cn-hangzhou.aliyuncs.com \
--docker-username=xxxxxxx \
--docker-password=xxxxxx5.3 查看Secrets
[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
aliyun-registry kubernetes.io/dockerconfigjson 1 16s
[root@kube-master secret]# kubectl describe secrets aliyun-registry
Name: aliyun-registry
Namespace: default
Labels: <none>
Annotations: <none>
Type: kubernetes.io/dockerconfigjson
Data
====
.dockerconfigjson: 173 bytes[root@kube-master secret]# kubectl get secrets
NAME TYPE DATA AGE
aliyun-registry kubernetes.io/dockerconfigjson 1 16s
[root@kube-master secret]# kubectl describe secrets aliyun-registry
Name: aliyun-registry
Namespace: default
Labels: <none>
Annotations: <none>
Type: kubernetes.io/dockerconfigjson
Data
====
.dockerconfigjson: 173 bytes5.4 创建ServiceAccount
5.4.1 不设置任何策略,测试是否能拉取私有仓库镜像
[root@kube-master secret]# cat pod-serviceaccount-secret.yaml
apiVersion: v1
kind: Pod
metadata:
name: stree-serviceaccount
spec:
containers:
- name: stree
image: registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1[root@kube-master secret]# cat pod-serviceaccount-secret.yaml
apiVersion: v1
kind: Pod
metadata:
name: stree-serviceaccount
spec:
containers:
- name: stree
image: registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1- 查看
[root@kube-master secret]# kubectl describe pod stree-serviceaccount
Events:
Type Reason Age From Message
---- ------ ---- ---- -------
Normal Scheduled 25s default-scheduler Successfully assigned default/stree-serviceaccount to kube-node01
Normal SandboxChanged 22s (x2 over 24s) kubelet Pod sandbox changed, it will be killed and re-created.
Normal BackOff 19s (x4 over 23s) kubelet Back-off pulling image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1"
Warning Failed 19s (x4 over 23s) kubelet Error: ImagePullBackOff
Normal Pulling 8s (x2 over 25s) kubelet Pulling image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1"
Warning Failed 7s (x2 over 24s) kubelet Failed to pull image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1": rpc error: code = Unknown desc = Error response from daemon: pull access denied for registry.cn-zhangjiakou.aliyuncs.com/hsuing/test, repository does not exist or may require 'docker login': denied: requested access to the resource is denied
Warning Failed 7s (x2 over 24s) kubelet Error: ErrImagePull[root@kube-master secret]# kubectl describe pod stree-serviceaccount
Events:
Type Reason Age From Message
---- ------ ---- ---- -------
Normal Scheduled 25s default-scheduler Successfully assigned default/stree-serviceaccount to kube-node01
Normal SandboxChanged 22s (x2 over 24s) kubelet Pod sandbox changed, it will be killed and re-created.
Normal BackOff 19s (x4 over 23s) kubelet Back-off pulling image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1"
Warning Failed 19s (x4 over 23s) kubelet Error: ImagePullBackOff
Normal Pulling 8s (x2 over 25s) kubelet Pulling image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1"
Warning Failed 7s (x2 over 24s) kubelet Failed to pull image "registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1": rpc error: code = Unknown desc = Error response from daemon: pull access denied for registry.cn-zhangjiakou.aliyuncs.com/hsuing/test, repository does not exist or may require 'docker login': denied: requested access to the resource is denied
Warning Failed 7s (x2 over 24s) kubelet Error: ErrImagePull5.4.2查看Pod,处于ErrImage
[root@kube-master secret]# kubectl get pod
NAME READY STATUS RESTARTS AGE
stree-serviceaccount 0/1 ImagePullBackOff 0 2m6s[root@kube-master secret]# kubectl get pod
NAME READY STATUS RESTARTS AGE
stree-serviceaccount 0/1 ImagePullBackOff 0 2m6s5.4.3 创建ServiceAccount
aliyun-registry是docker-registry类型的Secrets对象,由用户提前手动创建,它可以通过键值数据提供docker仓库服务器的地址,接入服务器的用户名,密码及用户的电子邮件信息等,认证通过后,引用ServiceAccount的Pod资源即可从指定的镜像仓库下载image
- 创建
[root@kube-master secret]# cat serviceaccount-imagepullsecret.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: imagepull-aliyun-sa
imagePullSecrets:
- name: aliyun-registry[root@kube-master secret]# cat serviceaccount-imagepullsecret.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: imagepull-aliyun-sa
imagePullSecrets:
- name: aliyun-registry- 查看
kubectl get sa imagepull-aliyun-sa -o yamlkubectl get sa imagepull-aliyun-sa -o yamlPod引用ServiceAccount
[root@kube-master secret]# cat pod-serviceaccount-secret.yaml
apiVersion: v1
kind: Pod
metadata:
name: stree-serviceaccount
spec:
serviceAccount: imagepull-aliyun-sa # 这里则是创建的sa的名称
containers:
- name: stree
image: registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1[root@kube-master secret]# cat pod-serviceaccount-secret.yaml
apiVersion: v1
kind: Pod
metadata:
name: stree-serviceaccount
spec:
serviceAccount: imagepull-aliyun-sa # 这里则是创建的sa的名称
containers:
- name: stree
image: registry.cn-zhangjiakou.aliyuncs.com/hsuing/test:v1- 查看
[root@kube-master secret]# kubectl get pod
NAME READY STATUS RESTARTS AGE
stree-serviceaccount 1/1 Running 0 3s[root@kube-master secret]# kubectl get pod
NAME READY STATUS RESTARTS AGE
stree-serviceaccount 1/1 Running 0 3s6. Secret实践
主要用于存储敏感信息,例如密码、秘钥、证书等
- 首先使用base64对数据进行编码
[root@k8s-master01 ~]# echo -n 'admin' | base64 #准备username
YWRtaW4=
[root@k8s-master01 ~]# echo -n '123456' | base64 #准备password
MTIzNDU2[root@k8s-master01 ~]# echo -n 'admin' | base64 #准备username
YWRtaW4=
[root@k8s-master01 ~]# echo -n '123456' | base64 #准备password
MTIzNDU22.接下来编写secret.yaml,并创建Secret
apiVersion: v1
kind: Secret
metadata:
name: secret
namespace: dev
type: Opaque
data:
username: YWRtaW4=
password: MTIzNDU2apiVersion: v1
kind: Secret
metadata:
name: secret
namespace: dev
type: Opaque
data:
username: YWRtaW4=
password: MTIzNDU2# 创建secret
[root@k8s-master01 ~]# kubectl create -f secret.yaml
secret/secret created
# 查看secret详情
[root@k8s-master01 ~]# kubectl describe secret secret -n dev
Name: secret
Namespace: dev
Labels: <none>
Annotations: <none>
Type: Opaque
Data
====
password: 6 bytes
username: 5 bytes# 创建secret
[root@k8s-master01 ~]# kubectl create -f secret.yaml
secret/secret created
# 查看secret详情
[root@k8s-master01 ~]# kubectl describe secret secret -n dev
Name: secret
Namespace: dev
Labels: <none>
Annotations: <none>
Type: Opaque
Data
====
password: 6 bytes
username: 5 bytes3.创建pod-secret.yaml,将上面创建的secret挂载进去:
apiVersion: v1
kind: Pod
metadata:
name: pod-secret
namespace: dev
spec:
containers:
- name: nginx
image: nginx:1.17.1
volumeMounts: # 将secret挂载到目录
- name: config
mountPath: /secret/config
volumes:
- name: config
secret:
secretName: secretapiVersion: v1
kind: Pod
metadata:
name: pod-secret
namespace: dev
spec:
containers:
- name: nginx
image: nginx:1.17.1
volumeMounts: # 将secret挂载到目录
- name: config
mountPath: /secret/config
volumes:
- name: config
secret:
secretName: secret# 创建pod
[root@k8s-master01 ~]# kubectl create -f pod-secret.yaml
pod/pod-secret created
# 查看pod
[root@k8s-master01 ~]# kubectl get pod pod-secret -n dev
NAME READY STATUS RESTARTS AGE
pod-secret 1/1 Running 0 2m28s
# 进入容器,查看secret信息,发现已经自动解码了
[root@k8s-master01 ~]# kubectl exec -it pod-secret /bin/sh -n dev
/ # ls /secret/config/
password username
/ # more /secret/config/username
admin
/ # more /secret/config/password
123456# 创建pod
[root@k8s-master01 ~]# kubectl create -f pod-secret.yaml
pod/pod-secret created
# 查看pod
[root@k8s-master01 ~]# kubectl get pod pod-secret -n dev
NAME READY STATUS RESTARTS AGE
pod-secret 1/1 Running 0 2m28s
# 进入容器,查看secret信息,发现已经自动解码了
[root@k8s-master01 ~]# kubectl exec -it pod-secret /bin/sh -n dev
/ # ls /secret/config/
password username
/ # more /secret/config/username
admin
/ # more /secret/config/password
123456